the rim self-data protocol
a deep dive on encryption, dissolution, and tacquing
This is a written companion to our HOPE 16 talk. It expands on the protocol concepts (Soradyne) at the heart of rim — how data lives on your body, how it's split, recombined, and shared — and points at where we're taking it next. The original slides are linked at the bottom.
why now
1.5 TB SD cards are $99. We're at the brink of a Cambrian explosion of wearables. Brain-computer interfaces are roughly a decade away from broad adoption. And the dominant business model for body-worn devices, data extraction, is unacceptable.
If we don't establish a foundation of tools — software and hardware — that respect the data on our bodies before that wave arrives, we won't be able to claw it back afterward. Free and open-source software got embedded in the server era (thank god) but missed the phone era. Wearables and implantables are the next wave. We're building essential fashionable pieces on free and open-source foundational infrastructure. Want to join?
the vocabulary
- Self Data
- An expansion of "personal data." Your message history, your heart rate, your video calls, your medical record, your 3D pose throughout time, your child's learning record. The kinds of data that are deeply personal to you and that you should be able to control, distribute, and grant or revoke access to without going through a third party.
- SD-core
- Wearing your storage out loud — SD cards as jewelry — to make a public, fashion-forward declaration that you have opted out of the data-extraction norms of the age. It's an aesthetic. Cyber-punk-esc but compatible with modern fashion. A 2010s retro future that is a radical tangibilization of data transfer from person to person physically. And the sense that it has a liberating feeling to do, complete privacy from the eyes of the Giants/Nations/Parents/Authority/Big Brothers, and showing off that it is that. It's a transgressive and intimate thing to do. Self-Data and Soul-Data backronymed to the SD in microSD.
- soradyne
- The proof-of-concept data protocol underneath rim. The name is "dinosaur" reversed (so it spells SD), with the implication baked in that it's already an outdated dinosaur — we hope it gets superseded quickly.
- dissolution / crystallization
- A piece of data is dissolved when it's split into encrypted shares spread across multiple devices, such that no single device reveals anything. It's crystallized when enough of those shares are pulled back together to reconstruct it.
- tacquing (also: tac, tactile, taquing)
- To transmit a live haptic connection to someone remotely. Telephones gave us audio across distance. The internet gave us video. We're at the start of a new era of wearables that will allow tactile communication across distance. "She'll call them" / "Let's FaceTime" / "Tac me."
SD-core: storage as fashion
SD cards are not the most durable storage medium, nor the cheapest, nor the fastest. But they are compact, standardized, recognizable in public consciousness, and they are just now reaching surprisingly large capacities at reasonable prices. A 1.5 TB microSD card fits in an earring.
That's three times the capacity of a typical laptop, in one ear. You can carry tens of terabytes of data on your person without effort. It cuts directly against the assumption that big-data corporations are necessary to host your personal data — you can host your own, on your body, quietly.
But we like to be loud about it. Putting your SD cards on your ears, around your neck, on your fingers says to the world: you have no idea what's on this. Google doesn't know what's on this. I have intentionally opted out of the data-vampiricism norms of this age.
the live self-data model
Here is the architecture, in one picture:
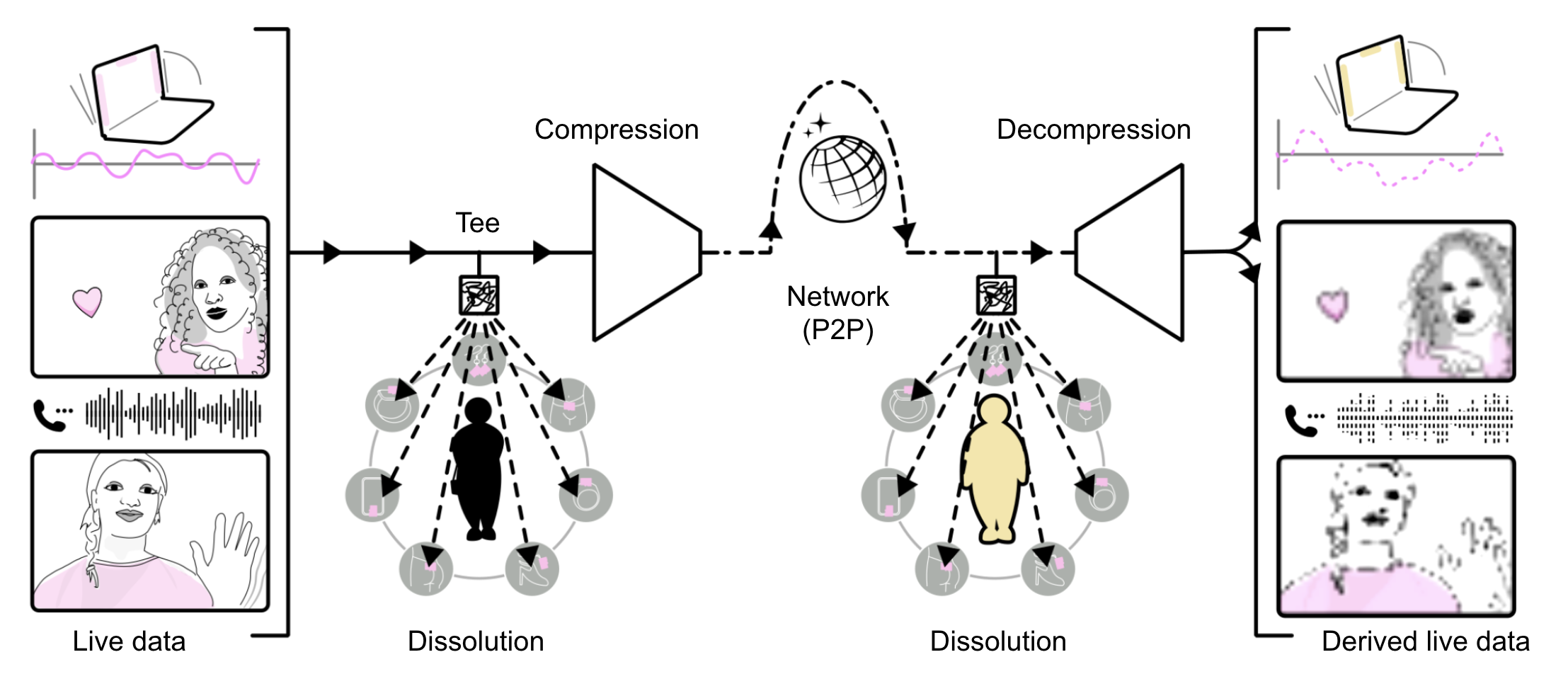
A self-data object is the basic unit of the protocol. Despite the name, it isn't an object in the object-oriented programming sense — it exists entirely as a synchronization procedure between peers. Self-data objects are asynchronous data flows.
The original data is stored locally via dissolution. When it needs to be sent, it's compressed and shipped over the network. On arrival, it's decompressed and dissolved into local storage on the receiving side. Peers use lightweight conflict-free replicated data types (CRDTs) to track where the shards live across the constellation of trusted devices.
what is received is not what is sent
An important property: in this model, what arrives on your screen is not the same bytes as what was sent. It's a derivation — a resampling appropriate to the receiver's display, the bandwidth available, the use case in that moment. You might get pixelated video, or a noisy audio reconstruction from a minimal data stream.
This isn't a quirk of compression; it's the worldview. Even when you open your phone and look at images "stored on your hard drive," you're not looking at the pixel data — you're looking at a resampling rendered for your screen, possibly at multiple resolution levels, possibly served remotely. All data is derived. So we don't try to copy literal data around and re-display it. We send the parts that are actually relevant for the use case at hand.
your body as storage and identity
Your physical devices become your storage and your cryptographic identity. The data is dissolved redundantly across the things you wear. To reconstruct anything sensitive, an attacker would need physical access to multiple items at the same time.
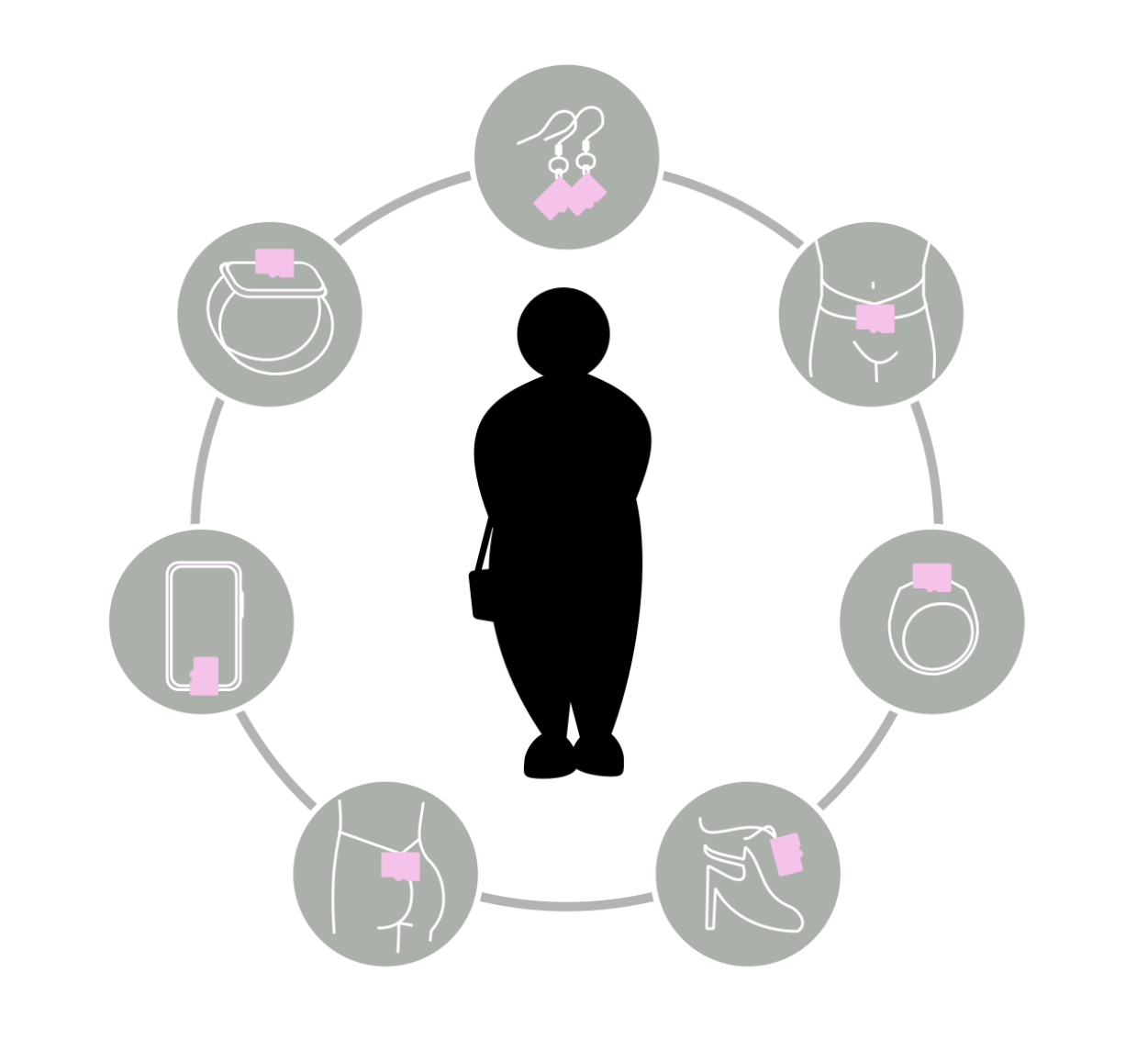
You can pick the threshold. Maybe you want any 3 of 5 devices or 4 of 7 devices to be enough to reconstruct your data. Different data types can use different thresholds simultaneously.
cascaded encryption
The dissolution implementation is a cascade of two cryptographic primitives:
- Shamir secret sharing on a small AES key. Information-theoretically secure, but it doesn't save space — every share is roughly the size of the secret.
- Reed-Solomon erasure coding on the AES-encrypted data block. Saves space (you can lose any n minus k shards and still recover) but is not by itself secure.
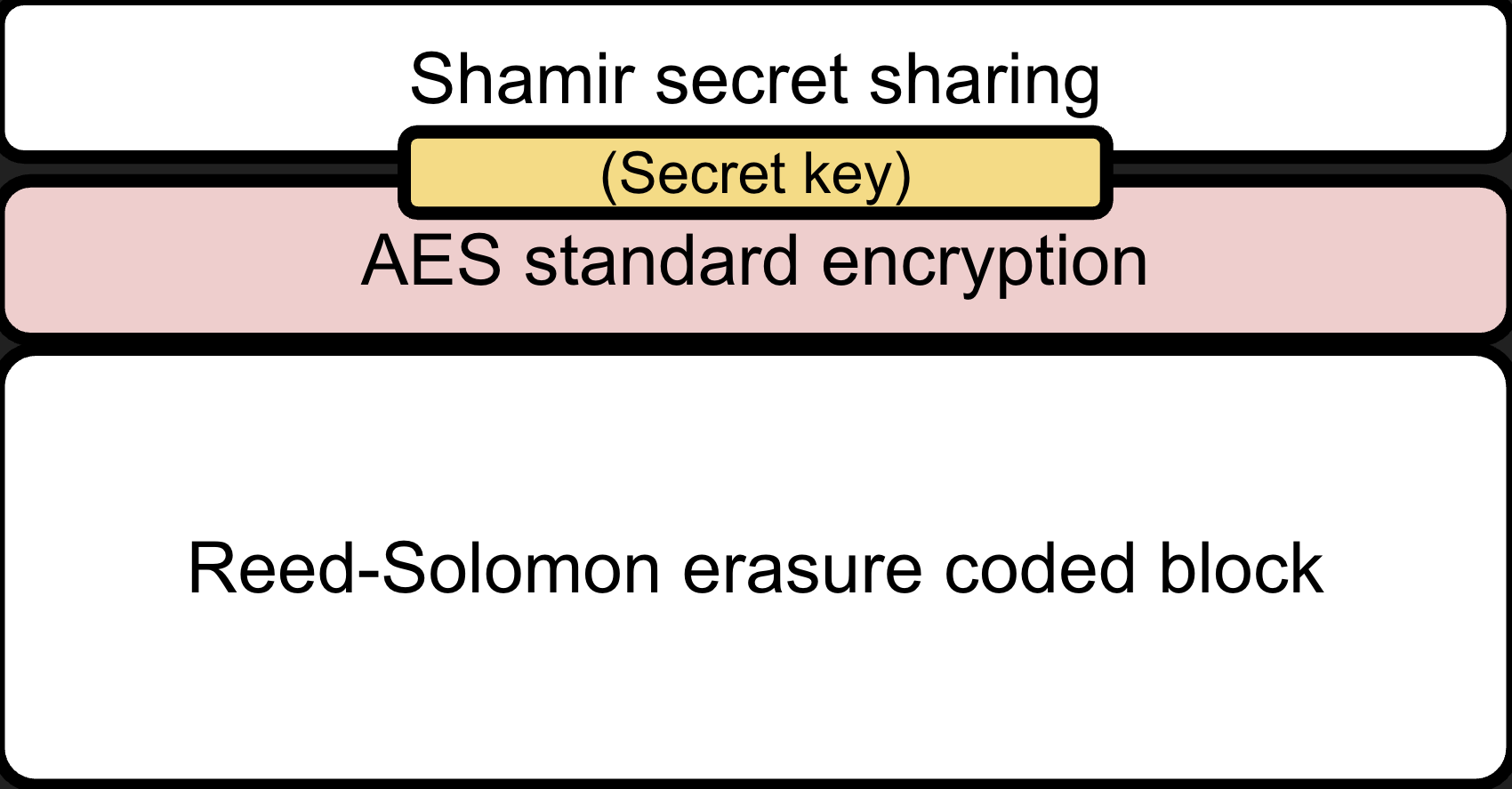
Each block of dissolved storage is a pair: a Shamir share of the secret key, and a Reed-Solomon shard of the encrypted data. Both are required, and both require the same threshold of pieces to reconstruct. They can be stored together on the same SD card, or on different devices entirely, or with different (k, n) parameters depending on whether you want more redundancy or more security for that piece of data.
Today, Soradyne supports storing them together on SD cards (or in local directories for testing) with a single shared (k, n). Differential parameters per block are possible but not yet implemented.
beyond cloud dependency
The traditional model: identity, storage, and data-loss recovery come from data giants and cloud providers. Lose your password? They reset it. Lose your phone? They re-issue your stuff.
The rim approach: your ecosystem of devices actively rebalances redundancy as devices come and go. A background process moves shares around to maintain your chosen threshold so the probability of total loss stays low. Because we have phones in our pockets, we are individually approaching multiple-nines uptime as servers. Whatever you might have thought you needed a cloud provider for, you can probably serve it yourself.
Serving a remote request from dissolved storage is then a matter of: query the CRDT shard registry, locate enough shards across your devices, reconstruct the relevant blocks, send them over an authenticated channel to the requester.
your data for you
This isn't just defensive. The point of carrying your data on your body is not only that nobody else can grab it — it's that you can do new things with it.
You can extract your Signal message history and visualize it as art you wear. You can show up to a doctor's office with your immunizations, allergies, and recent vital signs literally on your person, exchanged through a protocol you control. You can build a "goodness index" out of an algorithm you wrote yourself, tied to whatever signals correspond to your own happiness. You can carry your child's learning record so credentials can be derived from actual data rather than from third-party gradebooks.
You can imagine, ten or twenty years from now, having enough sensors that your 3D pose throughout time is recoverable, and a bodyworker — a massage therapist, a movement coach — who can see exactly when and how your tension habits formed, and help you work with them rather than against them.
but what if...
...you lose all your devices?
A fair worry, and the model extends to handle it. Beyond your wearables, the same dissolution scheme works at home: your own personal server, which could be also be paired with a local LLM. The things you wear regularly sync back to it, so a catastrophic loss of jewelry or quasi-wearables (aka your backpack) doesn't take all your data with it. It's still your hardware, on your premises, under your control. (For house-fire-grade redundancy: keep one share off-site, with someone you trust.)
...you get searched at the border, or stopped by police?
Another fair concern: data on your body means data that can be physically taken from you. But weigh that against the current default — Google or Apple handing your data to law enforcement on a warrant or subpoena, silently, going back years. Physical seizure is at least visible to you, bounded to what you happen to be wearing in that moment, and — with dissolution thresholds — typically still doesn't reveal much from any single piece. The cloud alternative is invisible and unbounded.
the long horizon
Tactile communication across distance — tacquing — is one step in a longer journey. The premise is that as we grow more connected through physical sensation, violence decreases between nations around the world. State propaganda becomes less believable. The public can't turn a blind eye to the government bombing the people whose hands they've held.
We deeply care about education. In 2017 we started developing *DAS, pronounced /STAR-dahs/, an open system that supports students in charting their own paths while tracking their own progress and evidence of learning.
presenting *DAS at the virtual HOPE 13 in 2020
*DAS stalled on the hard problem of how to securely manage data. Student learning data is among the richest fuel for third-party advertisers — it reveals what someone is most deeply passionate about. rim is that missing infrastructure. Once in place, *DAS comes back to life. We hope our future kids can learn more freely using this scaffolding.
Lastly, brain-computer interfaces (BCIs) are coming. They are deep-tech, expensive, and not democratically designed. We can't intervene at the BCI layer because by the time it arrives, the policy framework will have hardened. But we can build wearables now — accessible, hackable, fashionable, peer-to-peer — that act as training wheels for the policy and the cultural literacy we'll need when the deeper interfaces arrive.
status, and how to help
Soradyne is still a proof-of-concept. We don't use it for anything sensitive, yet. The codebase is rough; the security implementations need real review; there's a lot of plumbing missing.
What's working today: dissolution and crystallization with SD-card-backed block storage, CRDT-based shard tracking for shared self-data objects, a network bridge (currently insecure), demo apps in Flutter, utilities for SD setup and tests.
What's actively in progress: Bluetooth mesh networking for the body network, cryptographic signatures, hardening the dissolution implementation toward something real. The code lives at github.com/dgretton/soradyne. Issues, conversations, and (especially) cryptographic review are all welcome.
watch the original talk
HOPE 16, NYC, August 2025. Live demos, the haptic hinging laptop, the SD-card jewelry walkthrough, Soradyne technical dive, and long-term vision for rim.
HOPE 2025: rim — original full slide deck (PDF)
acknowledgements
in the spirit of "Democratic Design", one of our twelve pillars, we develop together with our community and fellow activists in the digital liberation movements. We make sure to give credit where it is due. Here's a list of folks who have helped develop the ideas and products of rim:
- 2026-04-29 · Chase · "unconditional compatibility" as name for pillar "interruptibility and instant reconnect, chaos nativity"
- 2026-04-08 · Anvita · tech art walks, advising on organizing, preparing, hosting, producing a fashion show
- 2026-03-24 · Karina · help with reviewing strategy and roadmap
- 2026-03-18 · Caitlyn · inspiration and co-organizing for a rim fashion show in September 2026
- 2026-03-15 · Elena · Writing Group Sundays
- 2025-01-01 · Meredith · privacy policy research
- 2025-12-15 · Caitlyn · ideas for rim jewelry: zipper, croc jibbitz, sewn into dress/skirt, braided hair clasp cuff charms (see design notebook)
- 2025-12-07 · Sara · nipple clamps, structural coloring piece, jewelry making and design
- 2025-12-07 · Emma · helping solder the rings on the gold parallelogram pendants
- 2025-12-07 · Katie · @chaindaddyyy collaboration for PolyDay Market
- 2025-12-06 · Cassie · view/apps as "skins"
- 2025-10-31 · Anvit · Yitong · hosting ARTPARTY, weekly checkins for a group of artists to showcase their work in early December, Emergence
- 2025-10-19 · Robin · setting up for jewelry workshop brunch
- 2025-10-19 · Lily · Morris · Maya · Yaqi · Robin · jewelry workshop brunch, live demos audience, glass beading, casting support
- 2025-10-18 · Zoda · encouragement to get low cost item on Etsy, earrings or necklace. Photoshoot at Noisebridge
- 2025-10-18 · Muffin · hacking bluetooth to SPI to SD card at Noisebridge. Suggestion to setup electroplating the PLA rims or branded side of microSDs
- 2025-09-18 · JLM · support and advising on presentation and speaking
- 2025-09-10 · Sonya · coined the term Hive Body like Hive Mind at NeuroNYC, and has since met up multiple times for discussions about clarifying and communicating the vision
- 2025-08-17 · Nora · logo design, workshops, aesthetics, sales, support at HOPE 2025 in NYC, designer of the five-charmed SD-core bracelet with arched chains
- 2025-08-17 · Changbai · Signal data visualizer coding, workshops, tabling support at HOPE 2025 in NYC
- 2025-08-16 · Dalcini · petabyte dress on NYC Fashion walkway, The Alexandria (named by Nora? Dana?)
- 2025-08-15 · HOPE organizers
- 2025-07-20 · Interlude · Sara · SD Corner, brainstorming names for the etsy store
- 2025-07-19 · Chuck · SD as "Soul-Data", connecting to Nick's rec to watch CJ the X's Bo Burnham vs Jeff Bezos
- 2025-07-07 · Andres · cryptography advising
- 2025-07-03 · Sara · nipple clamps as SD-Core jewelry
- 2025-06-12 · Wy · magnetic adapter sheet metal rim design around an SD card with beveled edges. Skull emblem that uses the SD card contacts as teeth of the skull.
- 2025-02-19 · Nora · rimg sizes can be a continuum from pinky to belt buckle and they will all each have a use (there is a range of sizes!)
some inspirational figures and their works
- Audrey Tang — served as the first Minister of Digital Affairs of Taiwan from August 2022 to May 2024. She helped deploy g0v's and vTaiwan civic-tech tools (including Pol.is) to draft participatory legislation for regulating uber in taiwan and other policies
- Nora Bateson — "warm data" contextualized, relational data that retains the network of meaning around it
- Shoshana Zuboff — The Age of Surveillance Capitalism, the foundational diagnosis of behavioral-surplus economics
- Giovanni Butarelli — "Privacy 2030" a manifesto for human-centered EU data law from the late European Data Protection Supervisor
- Jaron Lanier — Who Owns the Future?, an early argument that users should be paid for the data their lives produce
- Tristan Harris — Center for Humane Technology, a sustained public critique of attention extraction in consumer tech
- Wesley Ellis (tahnok) — open-source client for the Colmi R02 smart ring; backbone of our heart-rate demo
- Bunnie Huang — "On Hacking microSD Cards" seminal research into what's actually inside an SD card and what these chips can do beyond spec
- r/place — a 2017 Reddit-wide collaborative pixel canvas; an organic demonstration of distributed coordination at scale
- Polis — an opinion-clustering platform that surfaces consensus rather than amplifying polarization; central to Tang's work in Taiwan
And many many more whose imaginings and inspirations made these ideas possible to think. We all stand on the shoulders of giants standing on sand.
© 2026 Reclaim Intimate Mutuality LLC
